Operating System Security: Why It's Important and How to Protect Your Computer
Operating system security aims to defend the OS against various dangers, such as misconfigurations, remote intrusions, and malicious software like worms, trojan horses, and other viruses. It is crucial for the overall health of your computer as well. Effective malware and virus prevention makes programs run more quickly and smoothly by preventing viruses.
Why is Operating System Security important?
To safeguard personal data.
To safeguard organization assets.
To prevent data theft.
To stop malware and viruses.
Refraining from Unauthorized Access.
Cybersecurity in the current digital age
Data breaches and cyber threats are not new to the internet. Even more online threats have emerged due to the changes brought by the pandemic, including remote working, increased online business activity, and the migration to digital payment.
The transition to digital was sudden for many small organizations, leaving little time to enhance current security protocols or introduce new ones. Even larger organizations found it challenging to protect data while running remote teams and utilizing innovative tools like Trello, Slack, Flock, etc.
No system can be guaranteed to be completely secure. That is why Viruses, threats, and external access exist till now. The security of any system can be compromised in two ways:
1. Threat: A program that can potentially damage the system.
2. Attack: Attempts to break a security cover and access resources without permission.
There are two types of security violations - Malicious and Accidental. Malicious threats are harmful computer code or web scripts designed to cause a system failure. This allows anyone to enter the system from behind. Staying safe from Accidental Threats, for example, DDoS attacks, is comparatively easy.
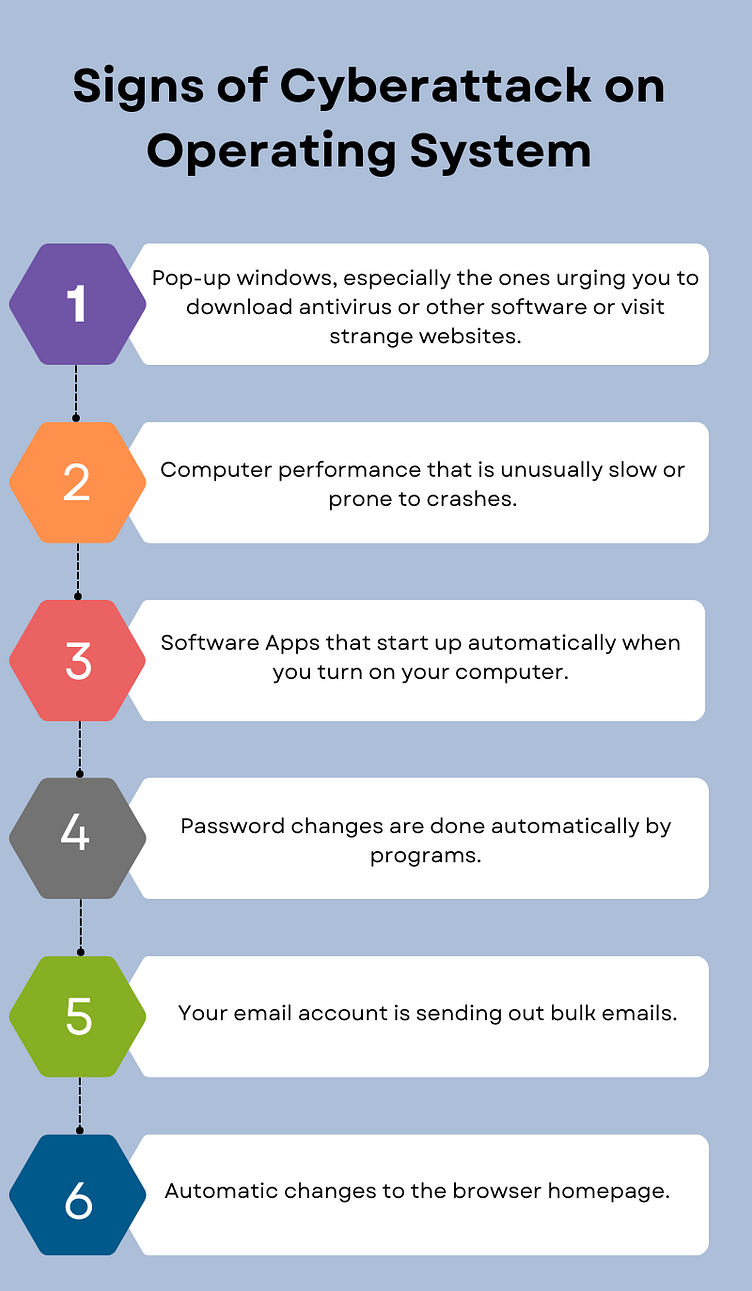
Any of the following types of security breaches can damage the system or access information without permission.

Aim of the Operating System Security
Updating the OS with regular patch updates.
Installing antivirus software and engine updates.
Using a security system to scrutinize all incoming and outgoing network traffic.
Establishing secure accounts with only the necessary permissions.
Types of threat
Now we will discuss types of program threats in detail and no one by one what their effects are and how they are implemented:
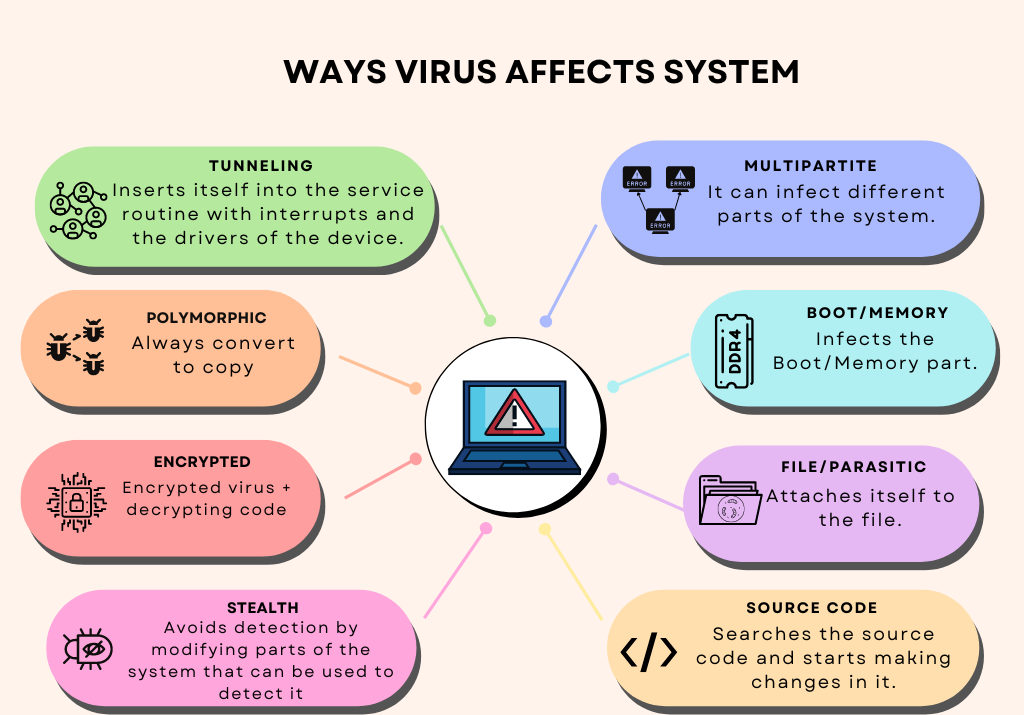
1. Virus - A self-infecting and malicious threat attaches itself to any system file and starts growing rapidly. It starts destroying all the necessary files and resources inside the network by modifying it.
2. Trap door - A program or system designer may mistake leaving specific paths that viruses can enter. It is not easy to detect and analyze because it requires looking at the source code of the entire system.
3. Malware - Malicious software, sometimes known as malware, includes a variety of attack methods, such as viruses, worms, trojan horses, and rootkits.
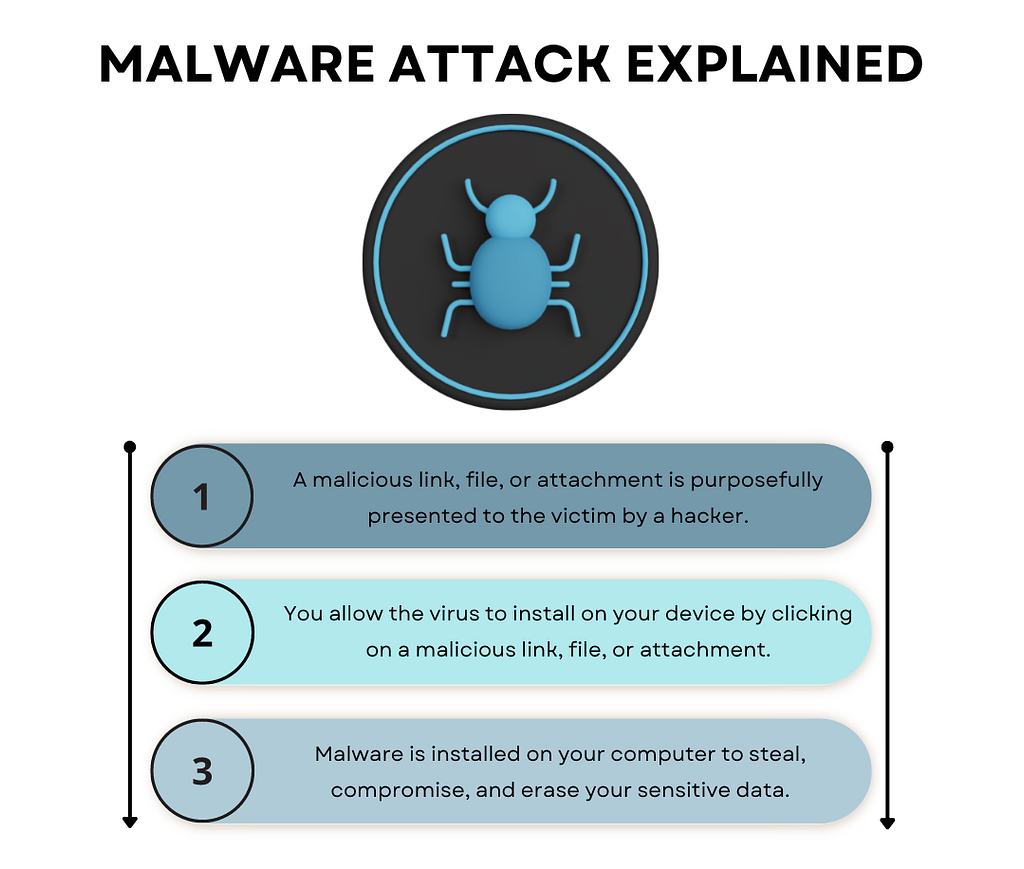
The highest percentage of infection since the SOES survey's start, malware activity that spread from employee to employee was experienced by 75% of firms in 2022.
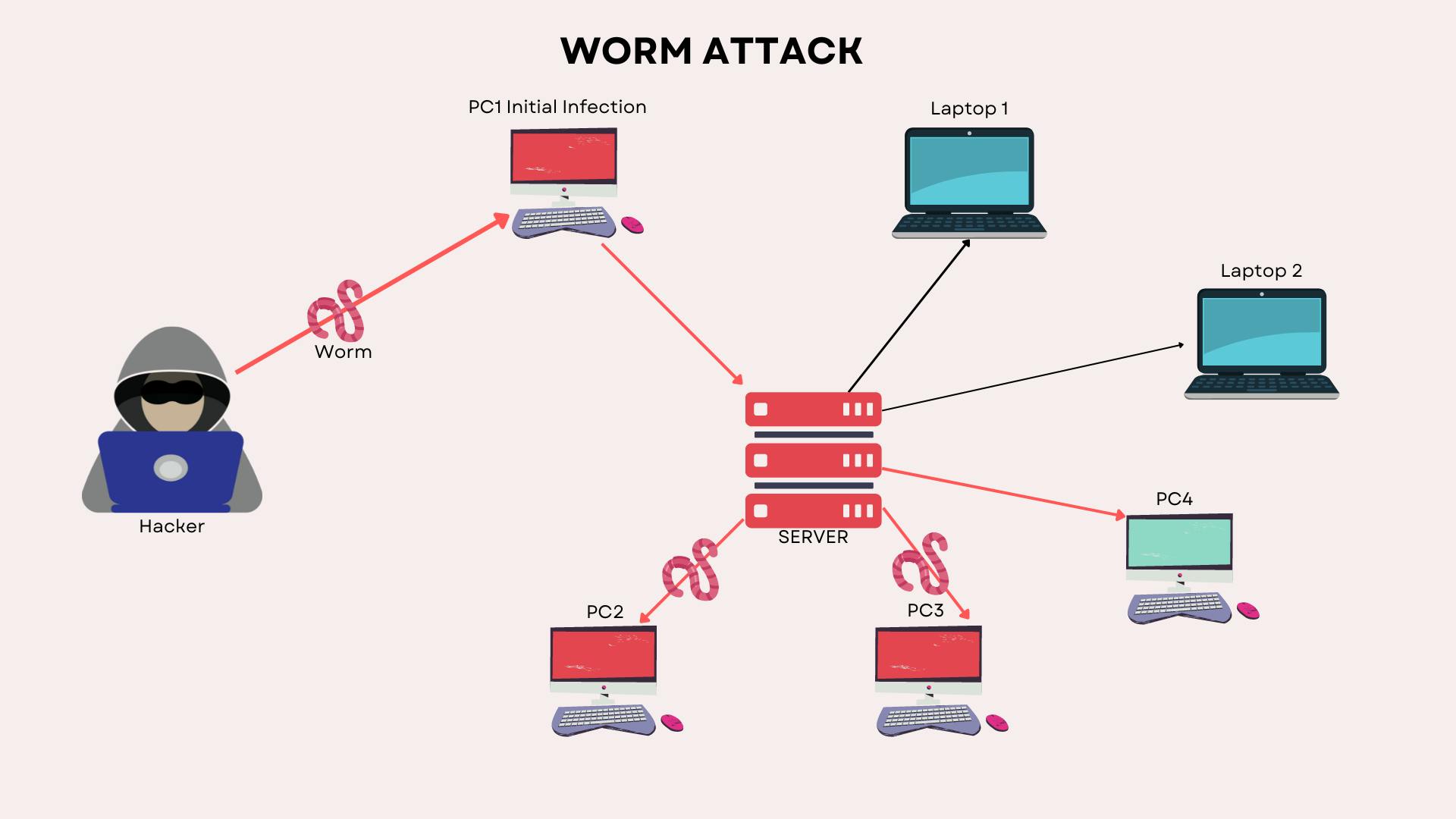
4. Worm - It is an infection program that has the power to spread from one network to another. The computer captured by the worm attacks the target system and writes a small program "hook" into it. By this hook, the worm is copied from that computer to the target computer. The functions of work can be seen in the picture below.
5. Port Scanning - This is a way to detect system vulnerabilities by hackers to attack later.
6. DoS Attack - A Denial of Service (DoS) attack aims to overload a system with continuous requests so it can no longer handle valid requests.

According to Cloudflare's DDoS threat report, DDoS attacks increased compared to last year.
7. Trojans - Hackers use this to steal user login credentials.

How can I safeguard my computer from these dangers?
Our main piece of advice for safeguarding your computer is to be mindful of the following:
Source of the email address.
What links are you clicking?
What are you downloading?
Your online behavior.
Online places where you are entering your data.

Conclusion
Security programs continue to develop new defenses against continuously growing security threats and new strategies for thwarting them. Understanding how to secure computer systems can address most other security issues, as most computer security problems are preventable.
